Cross-Chain Bridge Vulnerability Leads to $3M CrossCurve Loss
Losses at CrossCurve underline the high risk of cross-chain bridges during periods of rising crypto attacks.
CrossCurve halted user activity after an attack targeted its cross-chain bridge. The incident forced developers to investigate a smart contract flaw. Partner protocols and and security firms issued warnings as funds were traced on-chain.
User Interactions Halted as CrossCurve Examines Contract Weakness
CrossCurve confirmed on Sunday that its cross-chain bridge was targeted by attackers. The team linked the incident to a flaw in one of the bridge’s smart contracts. Users were asked to pause all activity while developers began reviewing the issue.
Because assets are held across multiple smart contracts, moving them between networks increases risk when a single component fails.
⚠️ URGENT Security Notice
Dear users,
Our bridge is currently under attack, involving the exploitation of a vulnerability in one of the smart contracts used.
Please pause all interactions with CrossCurve while the investigation is ongoing.
We appreciate your patience and… pic.twitter.com/yfo1KvWoDd
— CrossCurve (@crosscurvefi) February 1, 2026
Curve Finance addressed its community shortly after the incident. Users with exposure to CrossCurve pools were advised to reassess their positions and decide whether to withdraw voting support. The statement urged careful judgment when interacting with external protocols during unstable conditions.
Early checks found damage limited to the bridge, with no issues detected across other protocol components. Alerts went out quickly, while the team kept access paused and tracked the movement of stolen funds.
Protocol Calls for Asset Returns After On-Chain Review
After tracing on-chain activity, the team found that funds from the exploit had moved into 10 wallet addresses. CrossCurve said it could not confirm whether those wallets belonged to the attackers and saw no clear hostile behavior at that point. Even so, the protocol acknowledged that users lost funds due to the exploit.
In response, project officials appealed directly to recipients to return the assets. The team described the transfers as improper and asked for cooperation. To support recovery efforts, CrossCurve activated its SafeHarbor WhiteHat policy, offering a reward of up to 10% of recovered funds if the rest is returned.
Details included a direct contact email for coordination. An alternative option allows anonymous returns through a designated wallet address. The team said recovered funds would be returned to affected users after review.
Moreover, CrossCurve shared a contact email to help coordinate the return of funds. A separate wallet address was also provided for those who prefer to send assets back without revealing their identity. After verification, the team said it plans to distribute recovered funds to affected users.
Recent Breaches Expose Ongoing Risks in Decentralized Finance
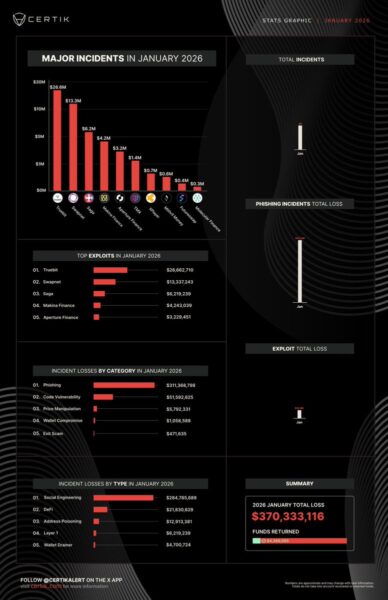
Crypto attacks have increased across the industry, with the CrossCurve incident adding to a growing list of breaches. Security firm CertiK recorded nearly $400 million in losses in January 2026, with more than 40 major incidents reported.
_Image Source: _X/CertiK
Cross-chain systems face a higher risk because they handle large amounts of funds and rely on complex structures. Recent incidents show how fast damage can spread once an exploit begins.
Other victims during the same period included Swapnet, which lost $13 million. Saga and Makina Finance reported losses of $6.2 million and $4.2 million. Step Finance also suffered a breach that drained several treasury and fee wallets, moving more than 261,000 SOL.
Losses across 2025 passed $1 billion, marking the worst year on record for crypto theft. The CrossCurve case adds another reminder of ongoing security gaps within decentralized finance.
Related Articles
Kelp DAO refutes LayerZero criticism; Aave bad debt reaches up to $230 million
DefiLlama denies exaggerated claims about the metrics, saying that Aave data has been excluded from the circulating liquidity calculation
Dune Analysis: 47% of LayerZero OApps Use Minimum 1-of-1 DVN Security Configuration
Claude Desktop Installation Reportedly Writes Backdoor File to Chromium-Based Browsers
Chinese National Arrested at Buenos Aires Airport for $49.4M Crypto Fraud Scheme
Lido EarnETH Vault Exposed to $21.6M rsETH Following Kelp Bridge Exploit, DAO Sets $3M Loss Protection