Sign Cross-Chain Protocol Explained: How Identity Interoperability Works Across Different Blockchains
As multi-chain ecosystems become the dominant trend in Web3, users often hold assets, interact with applications, and build identities across multiple blockchain networks. Traditional blockchain systems operate in isolation, which makes it difficult to share identity, contribution history, or on-chain reputation between chains. Sign’s cross-chain protocol is designed to solve this problem by allowing on-chain identity to move across network boundaries and enabling unified authentication and trusted verification.
From the perspective of Web3 infrastructure development, cross-chain identity protocols represent an important upgrade to digital identity systems. By standardizing identity credentials, behavioral records, and on-chain data, and enabling them to be verified across chains, Sign provides a composable identity layer for applications such as DeFi, DAO governance, GameFi, and social networks. This approach also helps build a more open and interconnected foundation for the Web3 ecosystem.
Definition and Importance of Cross-Chain Protocols
A cross-chain protocol refers to a technical framework that enables data and assets to move between different blockchains. Because each blockchain is designed with its own consensus mechanism and state structure, chains cannot directly share data by default. Cross-chain protocols therefore establish the communication and verification mechanisms required for interoperability.
In the early stages of Web3, most blockchain networks operated as isolated ecosystems. Assets, transaction histories, or identity data created on one chain could not be directly recognized on another. This fragmentation limited the scalability of blockchain applications and reduced the overall user experience.
As the multi-chain ecosystem has expanded, this issue has become increasingly prominent. For example:
-
A user may participate in DeFi on Ethereum
-
Engage with NFTs or GameFi on Solana
-
Conduct daily transactions on a Layer2 network
If each chain requires users to rebuild their identity and reputation from scratch, the process becomes inefficient and leads to data duplication and fragmentation.
For this reason, cross-chain protocols have gradually become a critical part of Web3 infrastructure. Beyond enabling asset transfers across chains, they also support the sharing of data, identity, and verifiable credentials, creating a unified connection layer for multi-chain ecosystems.
Sign’s Cross-Chain Architecture and Protocol Mechanism
The core design of Sign Protocol is its on-chain Attestation system. An attestation can be understood as a signed on-chain credential that records a verification made by one entity about a specific piece of information or identity.
For example:
-
A DAO verifying that an address is a member
-
A project confirming that a user participated in a specific event
-
A platform recording a user’s on-chain contributions
These attestations are stored on-chain and form structured, verifiable data.
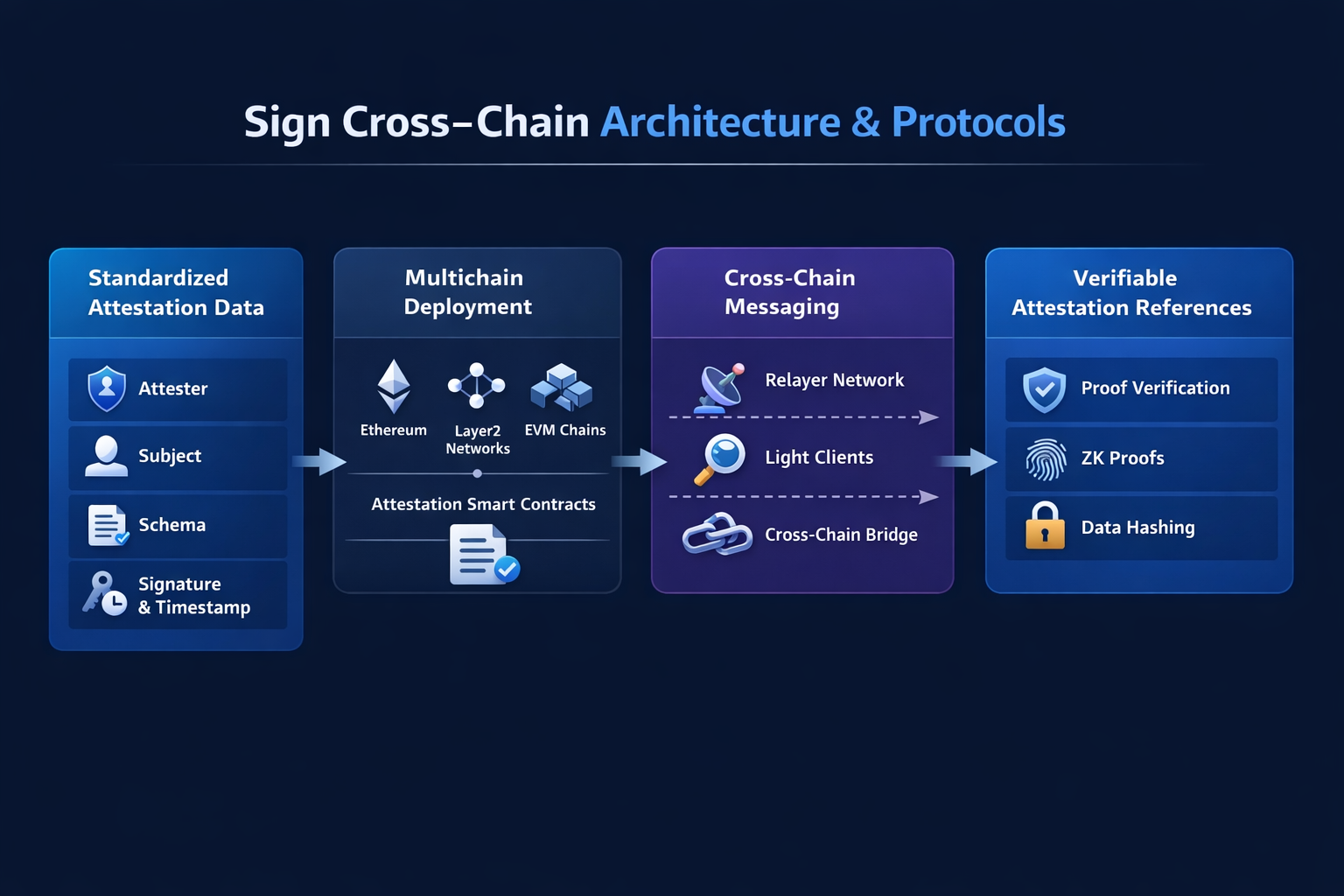
Within its cross-chain architecture, Sign enables identity interoperability through several mechanisms.
Standardized Attestation Data Structure
Sign abstracts identity credentials into a unified data format that includes:
-
Attester
-
Subject
-
Schema
-
Timestamp and signature
This standardized structure allows applications on different blockchains to recognize and interpret the data consistently.
Multi-Chain Deployment and Synchronization
Sign Protocol has been deployed across multiple blockchain networks, including:
-
Ethereum
-
Layer2 networks
-
Other EVM-compatible chains
By deploying protocol contracts on multiple chains, Sign can synchronize attestation data and allow applications across different networks to verify identity credentials.
Cross-Chain Messaging
To enable data interoperability, Sign uses cross-chain messaging mechanisms to transmit or reference attestation data between different chains. This approach typically combines:
-
Light client verification
-
Relayer networks
-
Cross-chain communication protocols
Together, these components ensure that the origin and authenticity of the data can be verified.
Verifiable Reference Mechanism
In some scenarios, Sign does not need to replicate the full dataset onto another chain. Instead, it allows applications to reference and verify the existence of data stored elsewhere. This approach reduces cross-chain costs while maintaining data integrity and trust.
How Cross-Chain Identity Verification Ensures Security and Privacy
Security is one of the biggest challenges for cross-chain systems. Historically, many blockchain attacks have targeted cross-chain bridges or interoperability protocols, making robust security design essential.
Sign addresses security in cross-chain identity verification through several mechanisms.
Cryptographic Signature Verification
Every attestation is signed by the attester and verified using cryptographic algorithms. This means identity credentials must be issued by trusted entities, otherwise they cannot be validated.
Immutable On-Chain Data
Because attestations are stored on blockchain networks, they cannot be altered once recorded. Any application verifying an identity can rely on the immutable on-chain record to confirm authenticity.
Permission and Schema Management
Sign uses Schemas to define the structure of different types of attestations. For example:
-
Identity verification schemas
-
DAO membership schemas
-
Event participation schemas
Each schema can include permission settings that restrict which entities are allowed to create or modify specific attestations.
Privacy Protection Mechanisms
In some scenarios, users may not want all identity information to be publicly visible. To address this, Sign supports:
-
Selective disclosure
-
Zero-knowledge proofs
-
Encrypted data storage
These mechanisms allow users to prove a qualification or identity attribute without revealing all underlying data.
Comparison Between Sign and Mainstream Cross-Chain Solutions
Multiple cross-chain technologies have emerged within the Web3 ecosystem, and Polkadot’s XCM is one of the more representative approaches.
The two systems differ significantly in design philosophy.
| Comparison Dimension | Sign Protocol | Polkadot XCM |
|---|---|---|
| Core Objective | Cross-chain identity and data attestations | General message communication between blockchains |
| Data Type | Attestation identity credentials | Arbitrary cross-chain messages |
| Application Focus | Web3 identity and reputation systems | Multi-chain ecosystem interoperability |
| Architecture Model | Protocol-level identity layer | Parachain communication protocol |
Polkadot XCM focuses on a low-level communication protocol designed to allow blockchains to exchange messages and share state. In contrast, Sign’s cross-chain mechanism is specifically designed for sharing identity and attestation data across chains. This makes it better suited as a dedicated identity infrastructure for Web3 rather than a general communication layer.
How Sign’s Cross-Chain Capabilities Support Web3 Ecosystem Growth
A cross-chain identity system can significantly improve interoperability between Web3 applications.
On the traditional Web2 internet, users typically access multiple services through unified account systems such as Google Login or Apple ID. In Web3, however, the isolation between blockchains has made this kind of unified identity difficult to achieve.
Sign’s cross-chain protocol introduces similar capabilities to the Web3 environment.
Unified On-Chain Identity
Users can use the same identity credentials across multiple blockchains, including:
-
DAO membership
-
NFT community identity
-
Contributor records
Composable Reputation Systems
When identity and behavioral records can be shared across chains, developers can build more sophisticated reputation models. Examples include:
-
DeFi credit scoring
-
DAO governance weighting
-
Web3 social influence metrics
Lower Development Barriers
Developers no longer need to build identity systems from scratch. Instead, they can directly use attestation data from Sign, accelerating application development.
Application Scenarios for Sign Across Multiple Blockchain Platforms
Sign’s cross-chain identity system can be applied across a variety of Web3 scenarios.
DAO Governance: DAOs can use Sign to record membership status, voting history, and contribution data, then share this information across multiple blockchains.
Airdrops and Community Incentives: Projects can distribute rewards based on a user’s on-chain activity, such as:
-
Participating in a testnet
-
Holding specific NFTs
-
Voting in governance proposals
These activity records can be verified across chains.
On-Chain Credit Systems: DeFi protocols can use attestations to build credit scoring models that support unsecured lending, risk assessment, and reputation systems.
Web3 Social Networks: User contribution records, community identities, and social relationships can all be verified through attestations and shared across multiple applications.
How Seamless Connections Between Blockchains Are Achieved
Achieving seamless cross-chain interoperability typically requires coordination across several technical layers.
-
Standardization of the identity data layer. Sign introduces a unified attestation schema that allows different blockchains to recognize identity-related data.
-
Cross-chain communication layer. Through relay networks or cross-chain messaging protocols, identity data can be synchronized or verified across chains.
-
Application layer integration. Developers integrate Sign’s SDK or smart contract interfaces into their applications in order to read and verify identity credentials.
Through this three-layer architecture, Sign enables a complete cross-chain workflow from data storage to application-level usage.
Future Development and Challenges for Sign’s Cross-Chain Protocol
Despite its strong potential, cross-chain identity technology still faces several challenges.
Cross-chain security risks: Because cross-chain systems are inherently complex, vulnerabilities in verification mechanisms could potentially lead to identity forgery or data manipulation.
Standardization issues: The Web3 ecosystem still lacks unified identity protocol standards, and different projects may use incompatible data formats or verification methods.
Privacy and compliance: As on-chain identity systems evolve, balancing transparency with privacy protection will become increasingly important.
Future development directions may include:
-
More advanced zero-knowledge proof technologies
-
Unified Web3 identity standards
-
Integration with real-world identity systems
These advancements will further accelerate the evolution of decentralized identity.
Conclusion
Sign Protocol’s cross-chain architecture introduces a new infrastructure path for Web3 identity systems. Through attestation mechanisms, cross-chain messaging, and standardized data structures, Sign enables identity interoperability between different blockchains and allows users’ on-chain identities and reputations to remain valid across multi-chain ecosystems.
As Web3 continues to move toward a multi-chain future, interoperability between identity, data, and applications will become increasingly important. Cross-chain identity protocols not only improve the user experience but also provide a trustworthy and composable foundation for DeFi, DAO governance, social networks, and the broader digital economy.
In the future Web3 landscape, cross-chain identity infrastructure such as Sign may serve as a key bridge connecting different blockchain networks and helping decentralized internet systems evolve toward a more open and collaborative architecture.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


